Table of Contents
Securing your devices
Key points:
Use strong passwords
Whether you have a computer with a traditional password, or a mobile device with a PIN, make sure the password or PIN you use to login to your device is strong. Same applies for all passwords for your online services.
Use a privacy screen / shield on your devices
If you use your computer, phone, or tablet in a public place — such as on a train, or in a café — buy a privacy screen for it.
A privacy screen is a sheet of plastic you place over your screen, which cuts down the viewing angle, meaning that people sitting next to you will find it harder to read your screen.
They are not perfect since, obviously, you still want to be able to see your screen when it is on.
You will get better protection against people sitting next to you than people sitting behind you, so you still need to think about how you are positioned.
Privacy screens are common for computers, and are increasingly common for phones, where they double as screen protectors.
For computers, I like the 3M “Gold” privacy screens.
Most computer privacy screens come with sticky tabs, so you can drop them into place easily.
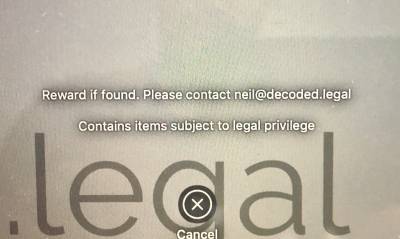
Put contact details on your device's lock screen
If you lose your device, you can increase the chances of getting it back by putting your contact details on your device's lock screen.
You could also state that it contains legally privileged information, if that might help avoid an unwanted search or seizure.
iOS
- Create a custom wallpaper of the right size for your device, containing the information you want (perhaps an email address or phone number (but not a phone number which only rings the device in question!))
- Transfer it to your device (e.g. AirDrop, or email, or iTunes file transfer)
- Make it your device's lock screen: Settings / Wallpaper / Choose a New Wallpaper / Set as lock screen.
macOS
- System Preferences / Security & Privacy / General / Show a message when the screen is locked
Limit what is shown on your lock screen
Many applications will let you preview messages when your device is locked — for example, the content of a text message, or the first line or two of an email.
If you lose your device, someone can still see information about you or your clients.
In particular, if you use your phone for two-factor authentication via a message, if that message pops up on the lock screen, someone who has stolen or found your phone would see that code.
Enable auto-wipe
If your device offers it, set it up to wipe automatically after sufficient incorrect password entries. However, make sure you take regular backups, as an annoyed child or curious toddler could, if left alone with your phone, wipe your device.
iOS
- Settings / Face ID & Passcode / Erase Data
Replace sensitive identifiers with pseudonyms
If you are reviewing a sensitive document, do you need to have the party names in it? If not, replace them with pseudonyms, so that someone who manages to see your screen gets less valuable information.
(This applies to physical documents too, if you're of the “print it out to review it” persuasion.)
Don't charge from public USB ports
The USB protocol carries both data and power so, when you plug your phone into a public USB port (e.g. at a café, train, or airport charging station), a malicious actor might be trying to connect to your device, as well as recharge it.
Use your own plug or battery pack
The safest thing to do is to charge only using your own plug / battery pack.
Use a USB data blocker
As an alternative, you can buy a USB data blocker — which some call as “USB condom” — which you connect between your device and the public USB port. These have the data lines cut, but still allow power to pass through.
Ideally, unlike the one in the photo here, your data blocker would be transparent, or easy to take apart, so you can verify that the data lines are cut.
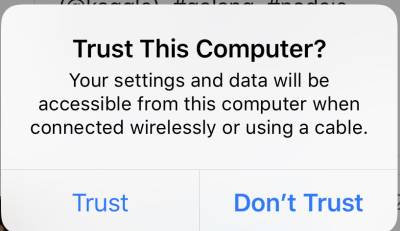
Device-based protection
Recent versions of the iOS software require you to put in your passcode before “trusting” a device to send information to, or read information from, your phone or tablet.
Only use your own cables
Although a cable may seem harmless, some cables are small computers in their own right, and some contain enough space in the housing (the plastic bits covering the connectors) to contain a malicious computer, which attempts to access your computer or phone when you connect it. (For example, see here.)
Some even contain tiny microphones, and SIM cards for relaying the audio back to an attacker.
Only use your own cables — do not borrow cables to charge your device — and, if you need a replacement cable, get it from a trusted source.
Cover your webcam when you are not using it
There's a strong chance that, right in front of your face, there is a camera. And there's an equally strong chance that it is unobscured the whole time.
Stick something in front of the camera when you are not using it.
You can buy very cheap plastic slider webcam covers, or even cheaper multi-use stickers. Depending on your laptop, you might find that stickers are a better bet as, being thinner, they are less likely to interfere with your laptop closing or staying shut.
At a pinch, there's always a sticky note.
Do not cover the "camera on" LED
Whatever you use, if you have an LED near the camera, which turns on when the camera is enabled (or, at least, should turn on when the camera is enabled), make sure that your sticker does not cover it, so you can see if the LED is on or not.
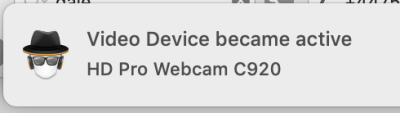
Disconnect your microphone or at least try to get a notification when it turns on
While it's easy to do something about a camera, it's much trickier to do something about a microphone. And, realistically, the potential of someone listening to what you are saying is a greater risk to security than being able to take a photo of you.
Hardware-based approaches
If you do not use the microphone at all, you could open your laptop and physically remove or disconnect it. Alternatively, you could see if plugging a jack plug which does not connect to anything into your computer's microphone port fools your computer into thinking that an external microphone is connected, disabling your internal microphone. However, as this type of disabling is normally done with software, someone within control over your computer might be able to work around this.
Software-based approaches
If you are not able to remove or disconnect your microphone, consider software which attempts to detect if your microphone is switched on and warn you.
For example, for macOS, Micro Snitch.
Only install software / apps from trusted sources
Part of cybersecurity is protecting yourself from external attackers. Another part is protecting yourself from software running on your own devices, passing your data to a third party.
Although it is not a guarantee that your apps or software are not doing something malicious, getting them from trusted vendors which offer a meaningful review can reduce your risk.
For example, for macOS or iOS, this is Apple's App Store.
If you do want to install software from outside a trusted source — and there is lots of great software which is not available through app stores — consider testing it on a spare machine first, and consider looking at its network traffic, to see if it is phoning home unnecessarily, or trying to exfiltrate data.
Check what permissions your software is requesting
When you install software, it may request your permission to access certain data or functionality of your device. For example, it might ask to access your address book, or to use your location.
Think about what the software is supposed to be doing for you, and consider (as best you can) whether those permissions are necessary.
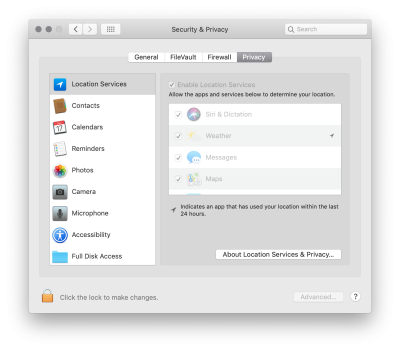
On macOS, you can see what software has requested which permissions, and what you have granted, in System Preferences / Security & Privacy / Privacy:
On iOS, it is Settings / Privacy:
Enable remote wipe functionality
If remote wipe functionality is available to you, set it up and learn how to use it.
Ideally, set up a test device and run through the process of wiping it. Write down what you did, and keep copies of that somewhere accessible.
Remote wipe requires communication to or from your lost device to trigger it. If someone immediately removes your device's SIM, or does not connect to the Internet, it is unlikely that your remote wipe will work.
Because of this, make sure you have a firmware password, have full disk encryption enabled, and that you are using a strong password.
Install software updates promptly
Responsible developers fix security problems in their software promptly. Not all developers are responsible, but you maximise your chances of having security problems plugged if you install software updates promptly.
There is a balance between security and usability, and software updates may break software functionality. So while the National Cyber Security Centre's guidance is to install software updates promptly, unless an immediate update is essential for fix a major security flaw, it might be worth waiting a few days after major updates are released, to see how other people react.
Before you install a major update to your computer's operating system, check that any software you rely on works with, and has been tested with, the updated version. Otherwise, while you might have the most up-to-date and secure operating system, your ability to use your computer productively could be severely impacted.
Enable auto-update if there is a low risk of incompatibility
For devices where an update is unlikely to break your workflow — perhaps your mobile device — consider enabling auto-update. That way, you never need to think about installing software updates yourself.
Keep a log of your key software, and alternative options
From a business continuity perspective, it is worth keeping a log of the software you rely on, and identifying an alternative so that, if your chosen software suddenly becomes unavailable or support is withdrawn, you have a fallback in mind.
Your fallback may not be perfect, but it should keep you working rather than panicking.
By the same token, be aware of locking yourself in to proprietary formats which does not offer easy export into common interchangeable formats: if you lock yourself into a particular format, moving to other software is support becomes unavailable might be difficult. If you can, storing data in a format which you can open with a different, replacement piece of software gives you greater control and flexibility.