Table of Contents
Using public Wi-Fi
It can often be convenient to connect to public Wi-Fi. But bear in mind that you are connecting to a fundamentally untrusted third party network.
Key points:
Provide fake details where you can
You'll often be asked for your title, name, and possibly even your address or other irrelevant information.
If you can get away with giving fake details (i.e. you can be comfortable that you are not committing an offence, such as fraud), it might be sensible to do so.
(Alternatively, you could read their terms of service, and their privacy notice, but there's no guarantee that they actually do what they say they do, and you're probably better of protecting yourself rather than relying on them anyway.)
If you have to give an email address, using a unique one
If you need to sign up with an email address, use a unique email address for that service.
Don't let your devices join public Wi-Fi networks automatically
Even if the connection is encrypted, you cannot be sure that it is a “genuine” access point, and not one run by a rogue third party. Anyone can set the broadcast name of a Wi-Fi network — what is known as the SSID — to anything they like.
So even if you see a network called “Starbucks”, for example, it might not be operated by Starbucks, and could just be someone sitting with a device in their bag, pretending to be the Starbucks network, trying to capture the traffic you send across their network.
If you permit your device to connect automatically to known networks, it may connect to a rogue network, and start sending data over to an unknown third party before you even realise it.
When you join a network, your operating system may prompt you to say if you want to “remember” the network, or join automatically in future. If it doesn't prompt you, you may need to go into your computer's settings, and tell it not to connect automatically.
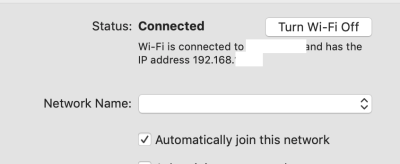
For example, in macOS, you need to untick the box “Automatically join this network”.
Run a VPN over the connection, as soon as you can
If you do want to use the Wi-Fi, run a VPN session over it. Or you could use Tor.
Some Wi-Fi networks block VPNs, and some block Tor. In those cases, don't use that Wi-Fi network — why would you want to trust a network which is trying to stop you operating securely? Consider tethering instead.
Wi-Fi which requires a login may not work if you use a VPN
Wi-Fi which requires a login page (a “captive portal”) may not work if your VPN is attempting to connect automatically. Typically, a captive portal requirse you to connect to it without going through your VPN, as you need to connect to their login page directly.
If you need to communicate with a “captive portal” without connecting to the VPN, that gives an opportunity for a malicious actor to acquire information from your device, or see where your device is trying to send traffic.
The best approach is to avoid these hotspots.
Connect using your phone instead
If you do not trust the network less than you trust your mobile network operator, you may be better off connecting your computer to the Internet via your phone's data plan. This is commonly known as “tethering”.
You might want to run a VPN, or use Tor, over the top of your mobile connection anyway.
You can normally tether via a USB cable, or else over Wi-Fi or Bluetooth. Using Wi-Fi or Bluetooth has the advantage that you can leave your phone in your pocket, but it comes at the cost of draining your phone's battery more quickly. Connecting via a cable is usually more reliable, but may drain your computer's battery more quickly, as it is probably charging your phone too.
Tethering on iOS
If you use an iPhone or iPad, rather than calling it “tethering”, Apple calls it “Personal Hotspot”. By default, this is turned off, but you can enable it in Settings / Personal Hotspot.
Guidance for setting it up is here.