Table of Contents
Your office Wi-Fi
Key points:
Make sure it is encrypted and not open
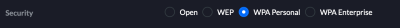
When you set up a Wi-Fi access point, you will be prompted to set the security you want in place.
Avoid “open” or “WEP”. If you have equipment which only works on WEP, upgrade it, because WEP is no longer effective and can be trivially broken. If you do not have equipment which only works on WEP, make a plan to move to WPA very soon.
For a small firm, “WPA Personal” is easy to administer, but you will need to change the Wi-Fi password when someone leaves, to prevent them from connecting to your network.
For larger organisations, “WPA Enterprise” is more likely to be suitable, but it requires a higher degree of IT knowledge to set it up.
Change all default passwords
If your network equipment comes with default passwords, make sure you have changed them.
If someone is able to access your Wi-Fi equipment, or your router, they could easily control the traffic on your network.
Disable access from the Internet
Unless you specifically need it (in which case, set it up securely), disable access to you Wi-Fi equipment / router from the Internet. This means both the administrative interface, and the devices themselves - if you do need to have remote access, plan it carefully, and lock it down (e.g. to specific IP addresses, lock out IP addresses if they get the username/password wrong more than a few times, add multi-factor authentication).
Use a firewall
Firewalls are devices (or software applications) which control what traffic is allowed to move between networks according to rules you set — for example, between the Internet and your office network.
Most consumer-grade routers do not have a firewall, and rely instead on something called “network address translation”. While this can have an effect a bit like a firewall, consider investing in a router with proper fireballing software. Pay someone to set it up securely for you, if you are not confident doing it yourself.
For example, a FireBrick is an affordable, versatile network applicable, which incorporates a firewall, and a tool for checking your firewall rules.
Make sure someone in the firm has the admin usernames and passwords, or admin access
Especially if you outsource your IT support, make sure someone in the firm has either a copy of all the usernames and passwords, or else admin access, and other information necessary to configure and control your Wi-Fi (and other elements of your firm's IT, for that matter).
You do not want to find that, if your IT support provider ceases to support you, you are unable to manage your network.
Have a means of preventing former staff from connecting to your network
If you have “enterprise grade” Wi-Fi equipment, you are probably authenticating users to your network by unique usernames and passwords, which can be readily revoked.
If, however, you are using consumer-grade equipment, and are using a common password for access to your Wi-Fi network, you'll need to think about how you deal with someone who leaves the firm: how do you make sure that they cannot continue to access your network. This might entail changing the network password, and distributing the new password to all remaining members of staff.
Only offer secure guest access
Offering guests — including clients — access to Wi-Fi may be nice, and perhaps even expected.
Only let guests connect to a network which is segregated (logically or physically) from your office network.
If you cannot do this securely, you are better off not offering it at all.
The same rule applies to employees connecting their own devices: do it securely, or ask them to use their own mobile phone connections.